Not ready for a demo?
Join us for a live product tour - available every Thursday at 8am PT/11 am ET
Schedule a demo
.svg)
No, I will lose this chance & potential revenue
x
x



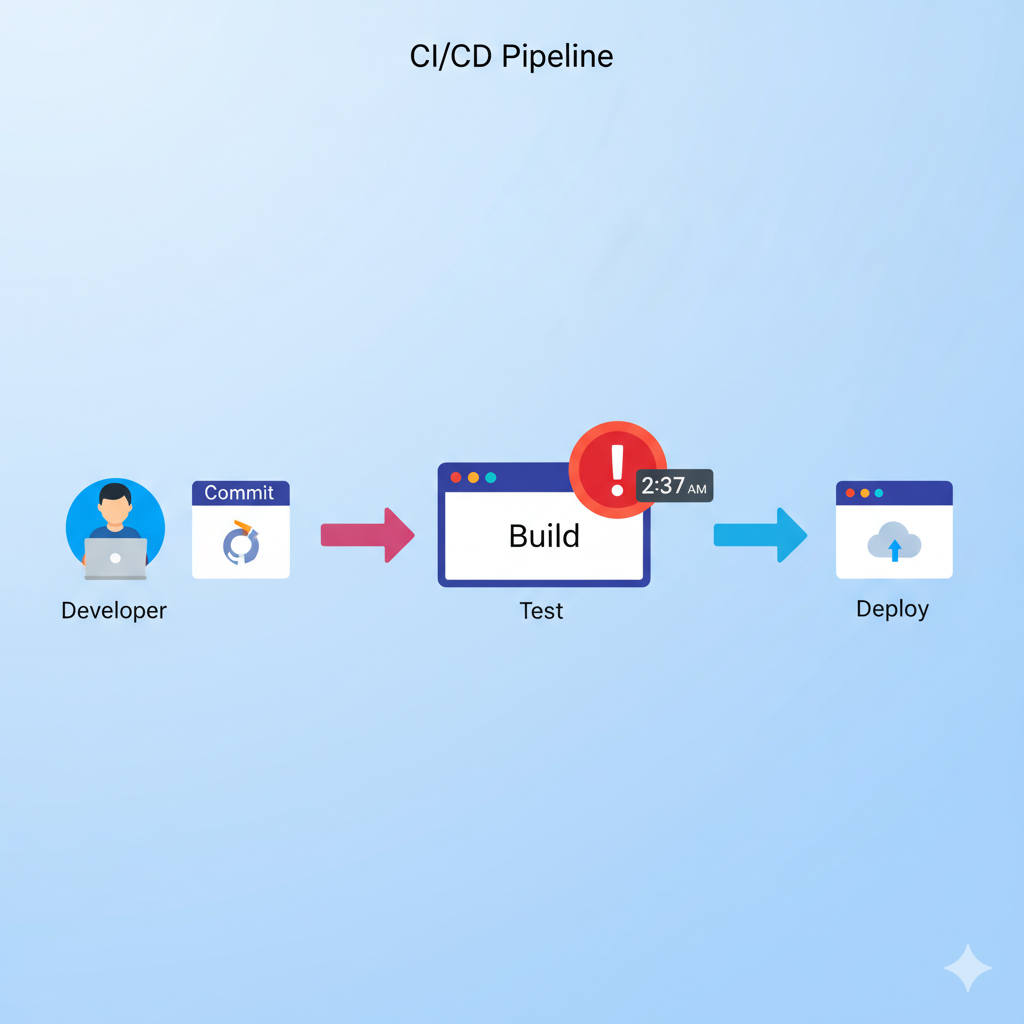
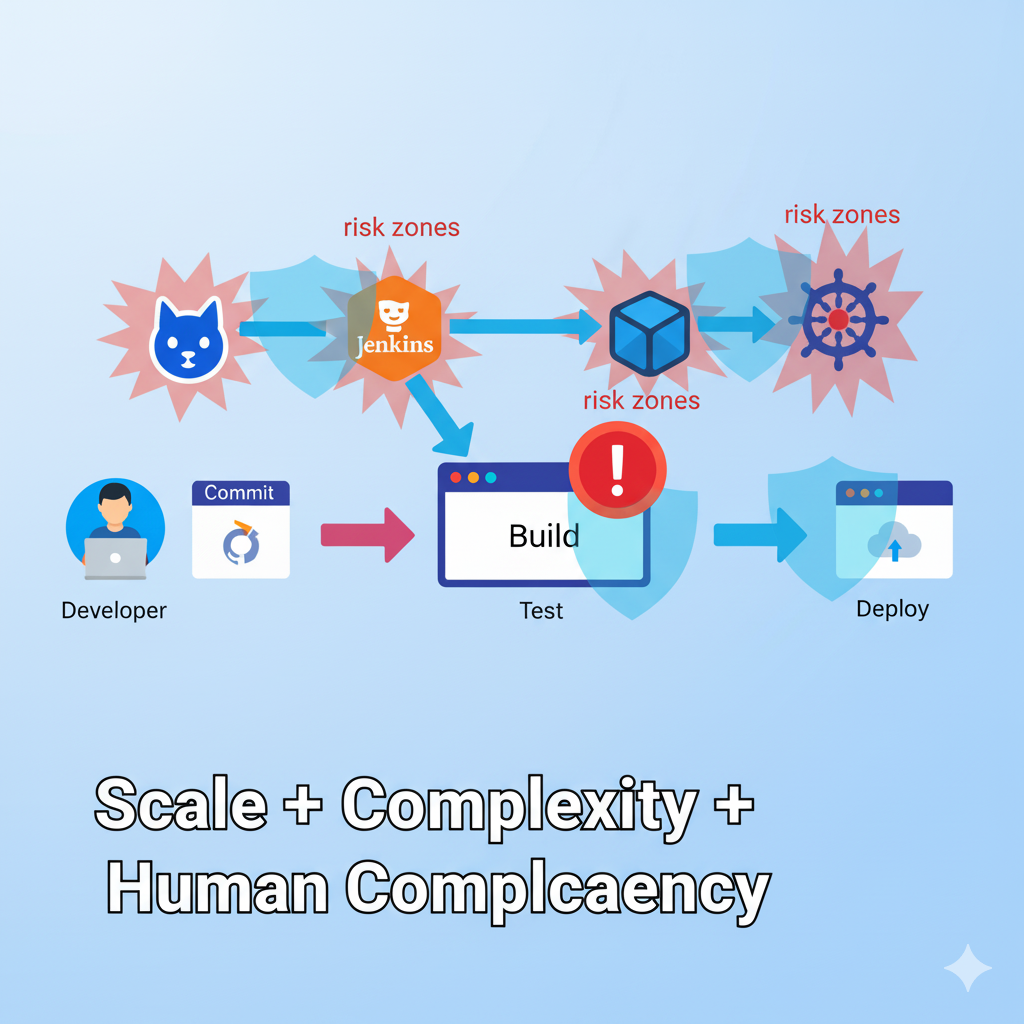
Automation powers CI/CD pipelines, cloud deployments, threat-detection tools, and infrastructure orchestration. It promises speed, consistency, and scalability, freeing teams from repetitive tasks.
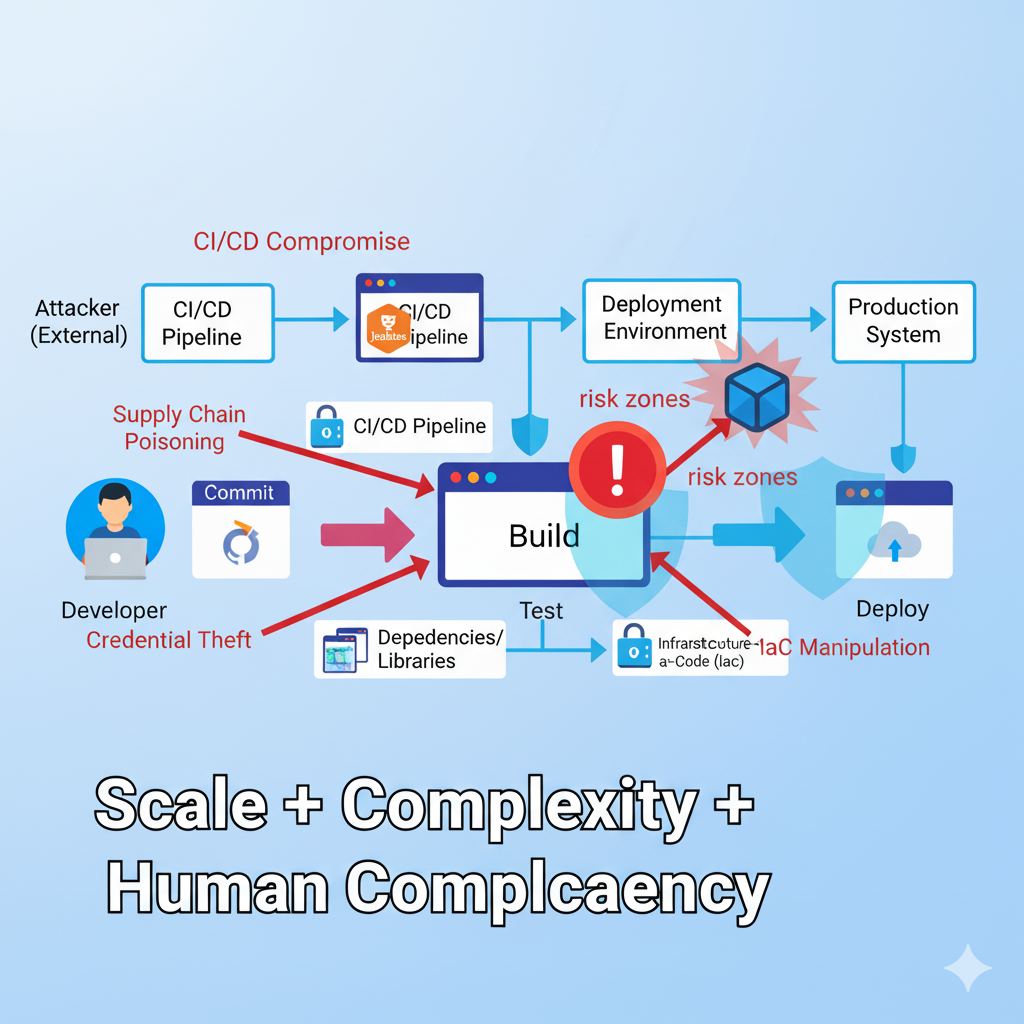
But attackers love automation too. They study it, mimic it, and sometimes turn your efficiency against you.
Automation is like a high-speed assembly line: one faulty component can compromise
everything downstream.
Attackers exploit weaknesses in automation’s speed and trust. Common pitfalls:
Scenario 1: 2:37 AM, Sunday, January 2023
AppSec Intervention:
Scenario 2: CircleCI 2023 breach
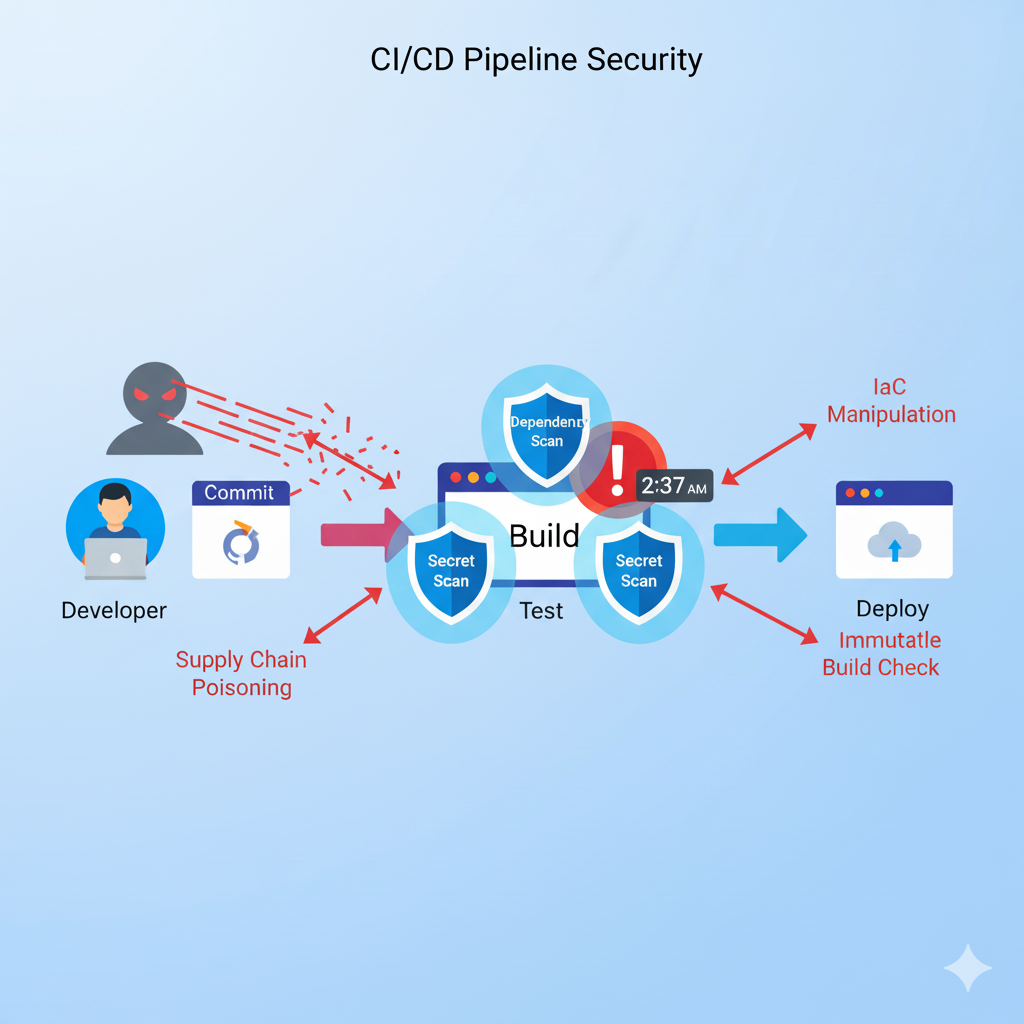
AppSec’s Role in Securing Automation
Application Security (AppSec) defends the entire automation pipeline, not just code.
Key interventions:
AppSec is your automation’s immune system.
Security early — SAST, dependency scanning, vulnerability checks before production.
Signed artifacts prevent undetected changes.
Ephemeral credentials, role-based access, secure vaults. Rotate keys regularly.
Isolate CI/CD agents and orchestration controllers. Limit Internet exposure.
Alert on unusual patterns: midnight builds, unexpected deploys, or new commit users.

Deploy to a subset first. Rollback automatically on anomalies.
Automation is indispensable, but attackers use it too. Layered defense is key:
Automation lets us defend at machine speed, but attackers have bots too. AppSec ensures we’re always one step ahead.”
Stay curious, proactive, and secure your pipelines like you guard your crown jewels.
Ready to master the strategies for securing automation and CI/CD pipelines discussed in this document? Start your journey with hands-on labs and expert-led courses on AppSecEngineer today.

Scenario: Early 2023, an e-commerce pipeline auto-deployed a dormant backdoor. Impact: Malware could have gone live across servers. AppSec Fix: SAST scans flagged suspicious logic. PR approval gates stopped deployment.
Scenario: 2:03 AM, developer commits a hard-coded API token. Impact: Attackers could hijack deployments. AppSec Fix: Secret scanning tools flagged the commit; vault-based credentials prevented misuse.
Scenario: Typo-squatted npm package fetched in nightly build. Impact: Malicious code could execute in production. AppSec Fix: Dependency allowlists and SBOM verification blocked it.
Scenario: Terraform scripts opened all firewall ports. Impact: Production exposed to the internet. AppSec Fix: Automated IaC scanning flagged issues. Peer review enforced changes.
cenario: 12:47 AM, compromised Jenkins plugin could inject malicious steps. Impact: Overnight builds deployed malware. AppSec Fix: Immutable job configs, plugin audits, and container signing blocked unauthorized changes.
Scenario: Attacker floods monitoring bots to hide exfiltration. Impact: Alerts silenced. AppSec Fix: Out-of-band logging and redundant SIEM pipelines caught anomalies.
Scenario: Service account with full deploy rights compromised. Impact: Single account could compromise production. AppSec Fix: Role-based access, ephemeral credentials, automated audits restricted permissions.
Scenario: Tests pass, but subtle malicious logic triggers in production. Impact: Automation alone misses threat. AppSec Fix: Multi-person approvals, staged deployments, and AppSec alerts ensured human verification.


.png)



Koushik M.
"Exceptional Hands-On Security Learning Platform"

Varunsainadh K.
"Practical Security Training with Real-World Labs"

Gaël Z.
"A new generation platform showing both attacks and remediations"

Nanak S.
"Best resource to learn for appsec and product security"
.svg)




.svg)



.png)



Koushik M.
"Exceptional Hands-On Security Learning Platform"

Varunsainadh K.
"Practical Security Training with Real-World Labs"

Gaël Z.
"A new generation platform showing both attacks and remediations"

Nanak S.
"Best resource to learn for appsec and product security"


.svg)
.svg)




United States11166 Fairfax Boulevard, 500, Fairfax, VA 22030
APAC
68 Circular Road, #02-01, 049422, Singapore
For Support write to help@appsecengineer.com



.svg)
